We install the Intel Remote Management Module (RMM) into all of our Intel server based deploys. If deploying a Tier 1 box we install theirs and make sure the KVM over IP option is enabled (license purchased).
Having out-of-band management access to a server can save critical time in the event of a server problem. We no longer need to jump in a vehicle and run down to our client’s site or have someone on-site for our remote clients.
Out of the box the RMM needs to be properly configured.
Once the server has been assembled and all of its components have had their firmware updated (Intel Download Site) we configure our RMM via the server board’s BIOS.
- Turn the server on and F2 into the BIOS.
- Server Management Tab.
- BMC LAN Configuration
- Set the IP for the RMM
- In the shop we leave it DHCP so that we can remote into the server while here.
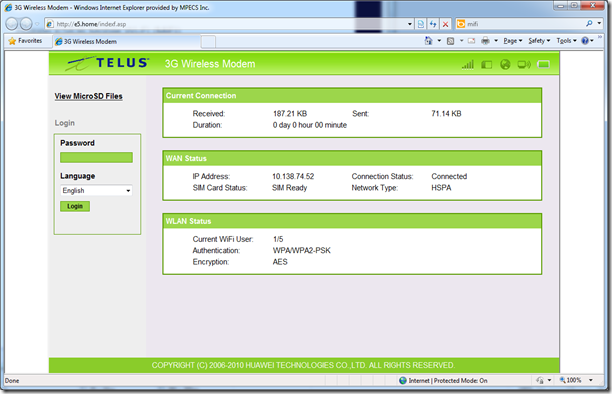
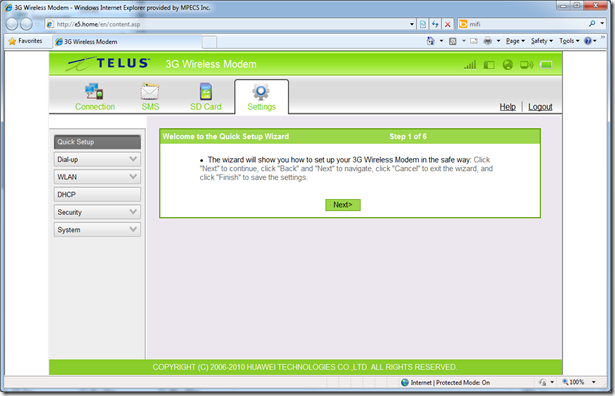
- Client’s site we tend to plug directly into the Internet and give it a static IP.
- Set the BMC DHCP Host Name
- Choose User ID and hit [Enter]
- Choose User3
- Privilege: Administrator
- User Status: Enabled
- Set the user name: JungleJim
- Set the user password: Icanacc3ssthis (x2)
- We end up with this.
- F10 to save settings and reboot the server.
If using DHCP then check the network’s DHCP Server console for the IP that the RMM has picked up.
Open a browser and navigate to the RMM IP.
Log on with the credentials set. Barring two left thumbs we should be able to log in.
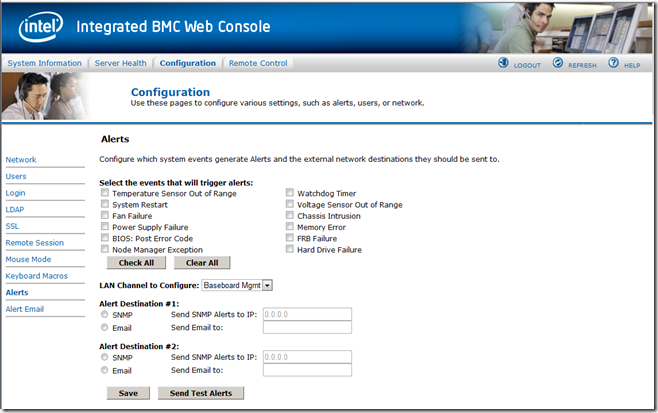
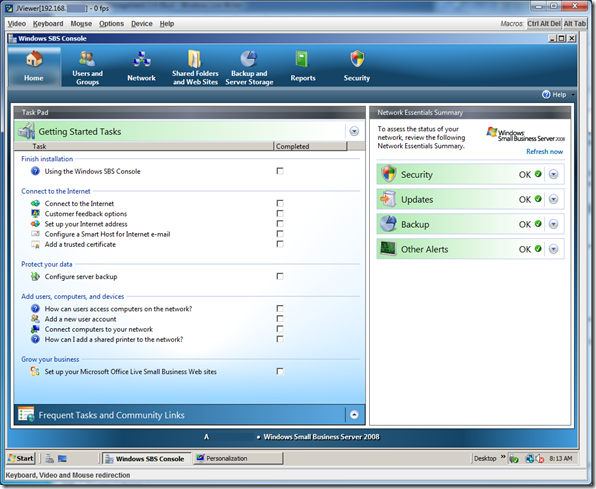
Once in we are able to launch the KVM over IP, reset the server’s power, power it up or down, and check the server’s current status.
The cost on the Intel units and Tier 1 equivalents will cover one on-site visit.
We believe that an RMM/iLO Advanced/iDRAC Enterprise and other remote management module should be a part of _every_ server configuration.
Philip Elder
MPECS Inc.
Microsoft Small Business Specialists
Co-Author: SBS 2008 Blueprint Book